Introduction
In computing a rootkit is a type of malware which resides deep within the operating system of the infected device. Rootkits often modify system files in order to conceal their appearance and prevent detection by security software.
Rootkits often act as entry points for future attacks including Trojans/Backdoors, Botnets,Ransomware and other types of malware preventing the user from easily removing the threat and even knowing that their system has been infected.
Use cases
Aside from use in malware rootkit technology is sometimes adapted for use in genuine applications, many on-demand antivirus tools will install modules deep into the operating system to prevent accidental removal or interference from other rogue software.
These features can help prevent rootkits from infecting the system in the first place, other non-hostile uses of rootkit technology include disk copying tools which cloak themselves as CD-ROM drivers. Other uses of the technology may also include anti-piracy systems which aim to prevent unauthorized copying of games.
Examples
Some notable examples of rootkits include the following:
Sony BMG Rootkit: This was a short lived anti-piracy system installed by Sony on a number of music disks which used rootkit capabilities to prevent removal of the software on users computers which had the potential to be exploited by malicious hackers to attack users computers.
Stuxnet: A rootkit believed to be developed by Israel and the United States which attacked Iranian SCADA controllers and disrupted enrichment processes. The worm utilized rootkit technology to stay hidden and avoid detection.
Protecting and removing rootkits
The best way to avoid rootkits is to keep your on-demand antivirus programs up-to-date and run regular scans, in addition it is paramount to keep your operating system updated with the latest security patches.
In addition you should be careful to install system-level software such as drivers from trusted sources to avoid installing potential rootkits. If your running Windows on your computer you can run a free tool called MBAR which can scan for and remove most Rootkits.
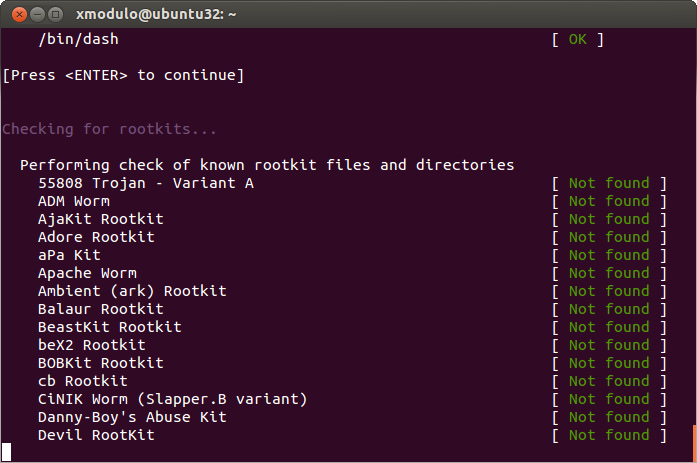
For Linux users you can install a package called Rkhunter which can help scan your system for common rootkits, the package checks hashes of system files to determine if system files have been modified which can be a sign of rootkit infection.
Conclusion
We hope you found this page to be a helpful resource, if so please share it with anyone you think would benefit and follow agrtech for new content updates.
Also be sure to check out our main blog, software utilities and business solutions.
Related pages from our technology glossary:
Best VPN services for torrenting
*Image credits
RootkitScan sourced from Flickr under Creative commons
![logo-new-23[1] logo-new-23[1]](https://agrtech.com.au/wp-content/uploads/elementor/thumbs/logo-new-231-qad2sqbr9f0wlvza81xod18hkirbk9apc0elfhpco4.png)