Introduction
Ransomware is a type of malware which seeks to disrupt a workstation or entire network and most importantly potential loss of important files.
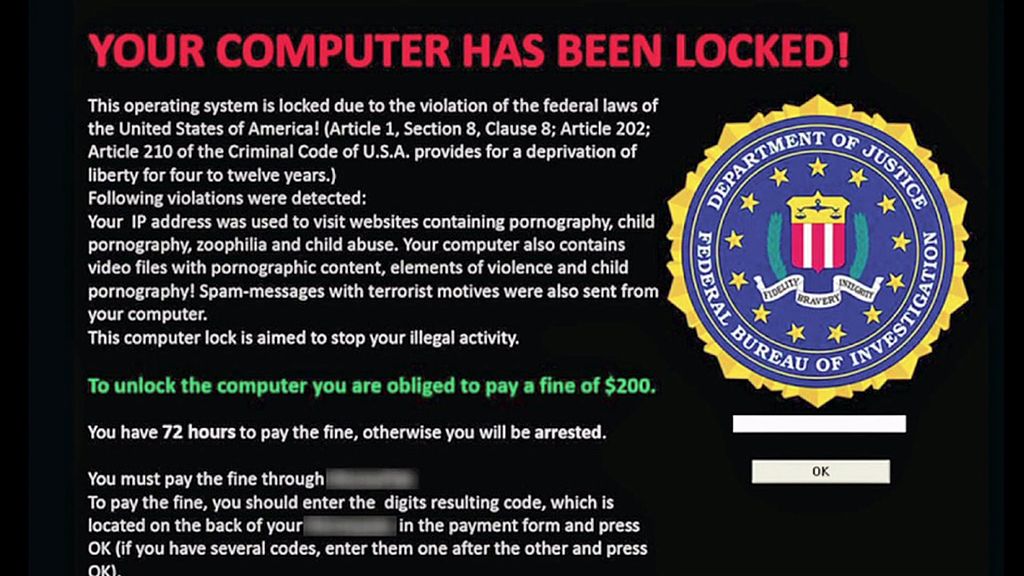
This type of malware can also lock down the computer and extorts the user for payment in order to continue using the computer.
Effects
While some older variants of this malware will act as an overlay or display fake popups many strains are far worse and will encrypt your data then hold it for ransom. These threats will threaten to destroy the data if the user doesn’t pay.
Often times attackers will use payment gateways such as Bitcoin, western union or other payment processors in an attempt to conceal their identity.
In the event of an attack it is not recommended to pay these criminals as this provides an incentive to continue these malware campaigns.
When it comes to this type of malware the most serious effect is losing important files and experiencing downtime due to damaged data.
Examples
There are many types of nasty ransomware which has been on the rise in recent years, here are a couple of notable variants.
- Cryptolocker: Spread in 2014 and caused widespread damage by encrypting local hard drives as well as network shares and other storage devices connected to a infected computer. Estimated by researchers to have made in excess of $30 million for the criminals who created the malware.
- Petya: Notable strain which was first discovered in 2016 targeting Windows. It encrypts data on drives and also infects the master boot record preventing Windows from starting and also has the capability to spread to other networked folders and drives.
- Locky: Primarily spread via emails purporting to be invoices and other documents. Locky also then proceeds to encrypt all data and changes file extensions to .locky to prevent users opening their files.
Protecting against this threat
The best defense against ransom malware is to keep your system up-to-date and maintain comprehensive backups of all your important data. Other steps you can take includes keeping offline backups, setting permissions to lock down certain computers and run regular anti-virus and anti-malware scans.
Recommended tools
Malwarebytes (Runs alongside existing anti-virus tools, premium version has built-in ransomware protection features)
Spybot anti-malware (Runs alongside other tools and apply extra security hardening measures to Windows)
Ransomfree (free tool to monitor for potential encryption attempts)
Conclusion
Overall the threats of this malware remain high making backups ever more important, hope this information has helped you. Be sure to share your comments down below and share the page with your friends.
Frequently Asked Questions From Around The Web:
How does Ransomware infect a computer?
Ransomware can infect a computer through malicious email attachments, compromised websites, or by exploiting vulnerabilities in software.
Can Ransomware affect mobile devices?
Yes while mobile based Ransomware attacks are very rare compared to desktop they do exist and can be found in fake apps or pirated apps shared on unsafe websites that are infected with Ransomware and potentially other types of threats targeting mobile.
Is it possible to decrypt files encrypted by Ransomware without paying?
In some cases, cybersecurity researchers or law enforcement agencies may release decryption tools that can help victims recover their files without paying the ransom. However, this is not guaranteed for all types of ransomware.
Can using a virtual private network (VPN) protect me from Ransomware?
While a VPN can provide a layer of security by encrypting your internet connection, it won’t necessarily protect you from Ransomware directly. It’s still crucial to follow good security practices and use antivirus software.
Should businesses be concerned about Ransomware attacks?
Yes, businesses are frequently targeted by Ransomware attacks due to the possibility of greater rewards. To counter the dangers, they should develop effective cybersecurity safeguards and data backup strategies.
Can Ransomware attacks be traced back to the attackers?
Because of the use of anonymizing technologies, cryptocurrencies for ransom payments, and sophisticated methodologies, Ransomware assaults can be difficult to track down. While some attackers have been identified, many remain unidentified.
Can my files be permanently lost if I don’t pay the ransom?
Not necessarily. While some Ransomware strains use strong encryption, security experts sometimes develop decryption tools over time. It’s possible to regain access to your files without paying, but it’s best to focus on prevention and backup strategies.
Related content from the AGR Technology glossary:
Buyers guide to choosing VPNs in Australia
Expert Penetration Testing Services in Australia
*Image credits
FBI Ransom image Motormille2 [CC BY-SA 4.0 (https://creativecommons.org/licenses/by-sa/4.0)], from Wikimedia Commons
Cryptolocker image sourced from Flickr under Creative commons
![logo-new-23[1] logo-new-23[1]](https://agrtech.com.au/wp-content/uploads/elementor/thumbs/logo-new-231-qad2sqbr9f0wlvza81xod18hkirbk9apc0elfhpco4.png)