Ransomware is no longer just an IT problem. It is a business continuity problem, a financial risk, and in many cases, a reputational one too. For organisations of all sizes, one weak password, one missed patch, or one convincing phishing email can be enough to disrupt operations fast.
At AGR Technology, we help businesses strengthen their ransomware defence with practical, layered strategies that cover prevention, early detection, incident response, and recovery. This page explains how modern ransomware attacks happen, what strong protection actually looks like, and where expert support can reduce risk before a serious incident occurs.
If you need help improving cyber resilience, reviewing your current controls, or building a more secure IT environment, our team can help.
Get in touch with our team to find out how we can assist with your Cyber security needs
What our clients are saying
Why Ransomware Remains A Critical Business Threat
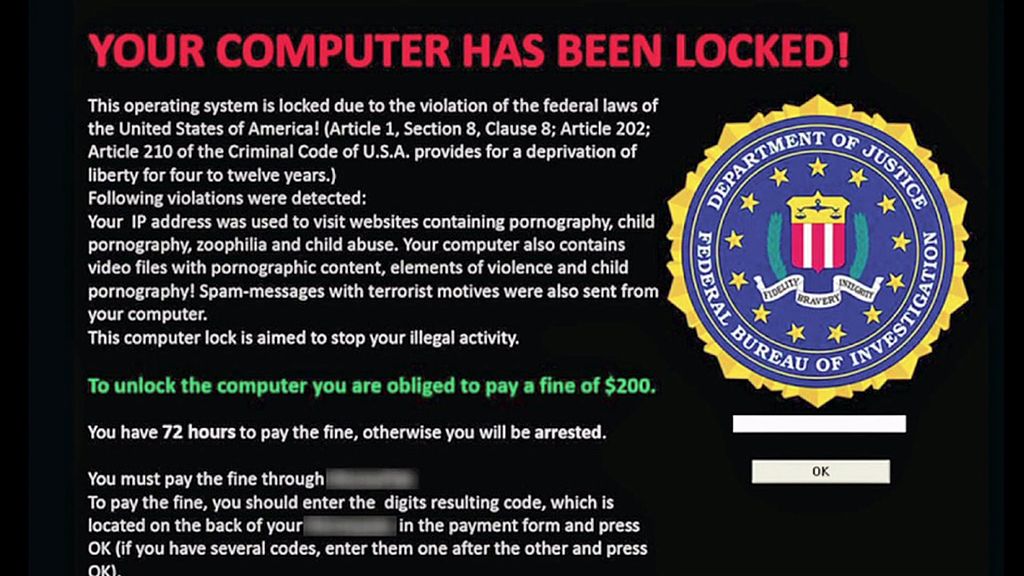
(Example image of a Ransomware malware that impersonated the FBI in the United States)
Ransomware remains one of the most disruptive cyber threats facing modern businesses because it targets what organisations rely on most: access to systems, operational continuity, and trusted data. Attackers are not just locking files anymore. They are stealing sensitive information, moving laterally through networks, targeting backups, and pressuring businesses with extortion tactics that can affect customers, staff, suppliers, and regulators.
The risk is not limited to large enterprises. Small and mid-sized businesses are often targeted because they may have fewer internal security resources, inconsistent patching, weaker access controls, or limited incident response planning. And for larger organisations, complexity itself becomes a risk. More users, more endpoints, more software, and more third-party integrations can create more paths for attackers to exploit.
A ransomware incident can lead to:
- Operational outages and service disruption
- Loss of access to critical business systems
- Data theft and privacy exposure
- Revenue loss and recovery costs
- Compliance and legal complications
- Damage to customer trust and brand reputation
According to guidance from the Australian Cyber Security Centre and global agencies such as CISA, ransomware continues to evolve because it works financially for attackers. That is why effective ransomware defence needs to be ongoing, not treated as a one-off project.
At AGR Technology, we approach ransomware protection as part of a broader business risk strategy. That means aligning cyber security controls with your systems, users, workflows, and recovery priorities, not just installing tools and hoping for the best.
If your business is reviewing its security posture, now is the right time to assess where the biggest gaps are and put stronger safeguards in place.
How Modern Ransomware Attacks Typically Unfold
Modern ransomware attacks are usually not random. In many cases, they are planned, multi-stage intrusions designed to gain access quietly, expand privileges, disable protections, and then encrypt or exfiltrate data at the point of maximum impact.
Understanding how these attacks unfold helps businesses make better decisions about prevention, monitoring, and response.
Common Entry Points And High-Risk Weaknesses
Most ransomware incidents begin with a preventable weakness. Common entry points include:
- Phishing emails carrying malicious links or attachments
- Stolen or weak credentials, especially where multi-factor authentication is missing
- Exposed remote desktop services or poorly secured remote access tools
- Unpatched operating systems, applications, firewalls, or VPN appliances
- Third-party software vulnerabilities and supply chain exposures
- Misconfigured cloud environments or excessive user permissions
Once inside, attackers often try to escalate privileges, move across the network, identify valuable systems, and locate backups. In more advanced attacks, they may spend days or weeks inside the environment before launching encryption.
This is why a single security product is rarely enough. Strong ransomware prevention depends on layered security controls, visibility, and disciplined operational processes.
Business Impacts Beyond Downtime And Data Loss
The immediate disruption of encrypted systems is only part of the problem. The broader business impact often includes:
- Delayed service delivery and missed client commitments
- Interrupted finance, payroll, logistics, or customer support functions
- Costly forensic investigations and remediation work
- Internal productivity loss across multiple teams
- Contractual issues with partners or clients
- Insurance, legal, and notification obligations where data is exposed
And there is another issue many businesses underestimate: recovery confidence. Even after systems come back online, leadership still needs to know whether the restored environment is clean, whether data has been altered, and whether the same weakness remains exploitable.
That is why our ransomware defence services focus on more than just blocking attacks. We help businesses improve readiness across security architecture, system hardening, recovery planning, and response procedures so they can reduce uncertainty when it matters most.
If your current setup has grown over time without a clear security review, we can help assess the weak points before an attacker finds them first.
How To Prevent Ransomware Before It Spreads
Prevention remains the most cost-effective ransomware strategy. While no environment can be guaranteed risk-free, strong preventive controls can significantly reduce the likelihood of compromise and limit how far an attacker can move if they get in.
At AGR Technology, we focus on practical ransomware prevention measures that fit real business environments rather than generic checklists.
Strengthening Access Controls, Endpoints, And Email Security
A large portion of ransomware activity still starts with compromised access or malicious email content. The basics matter, but they need to be done properly.
Key prevention measures include:
- Enforcing multi-factor authentication across critical systems
- Removing shared accounts and tightening privileged access
- Applying least-privilege access so users only have what they need
- Hardening endpoints with managed protection, application control, and monitoring
- Filtering phishing emails, malicious links, and suspicious attachments
- Disabling risky macros and restricting unnecessary script execution
- Providing regular staff awareness training based on real attack patterns
Good security awareness training is especially important because users are often the first line of defence. But training works best when paired with technical controls. People are busy. Mistakes happen. Your systems should be designed with that reality in mind.
Building Resilience With Patch Management, Segmentation, And Backups
Once attackers gain access, they look for ways to spread. That is where infrastructure hygiene becomes critical.
We recommend prioritising:
- Timely patching of operating systems, applications, network devices, and internet-facing services
- Network segmentation to limit lateral movement between systems and departments
- Secure configuration baselines for servers, endpoints, and cloud services
- Continuous review of exposed services and unnecessary open ports
- Backup strategies that include offline, immutable, or otherwise protected copies
- Regular backup testing to confirm data can actually be restored
Backups deserve special attention. Many businesses assume they are protected because backups exist, but the real question is whether those backups are isolated, current, tested, and recoverable under pressure. If they are connected to the same environment without proper safeguards, ransomware may reach them too.
Our team can help businesses review backup architecture, endpoint security, access controls, and patch management processes as part of a broader ransomware prevention plan. If you want a clearer view of your current risk, contact AGR Technology for a practical security review.
How To Detect Ransomware Early And Respond Fast
Early detection can make the difference between a contained security event and a major business disruption. The longer ransomware operators remain undetected, the more time they have to escalate privileges, identify high-value assets, disable protections, and prepare for encryption or data theft.
That is why ransomware detection should not rely on one alert source alone. Businesses need endpoint visibility, log monitoring, anomaly detection, and a clear response process.
Warning Signs Security Teams Should Never Ignore
Ransomware activity often leaves signals before full encryption begins. Common warning signs include:
- Unusual login behaviour or impossible travel events
- Repeated failed login attempts or suspicious account lockouts
- New administrative accounts appearing unexpectedly
- Sudden disabling of antivirus, EDR, logging, or backup services
- Spikes in file renaming, encryption-like activity, or mass file access
- Suspicious PowerShell, command-line, or remote management activity
- Unexpected outbound traffic or large data transfers
- Ransom notes, inaccessible files, or unusual file extensions
Some of these signs can look minor in isolation. Together, they may indicate an active intrusion. That is why alert triage and contextual review matter so much.
Immediate Containment Steps During An Active Incident
When ransomware is suspected, response speed matters. The initial goal is containment, not perfection.
Immediate steps often include:
- Isolating affected devices from the network
- Disabling compromised accounts and privileged credentials
- Blocking known malicious IPs, domains, or remote sessions
- Preserving logs and forensic evidence
- Identifying the scope of affected systems, users, and data
- Confirming the status of backups and critical infrastructure
- Escalating to internal leadership and external security support
Businesses should avoid impulsive actions that destroy evidence or make recovery harder. For example, wiping systems too early or rebooting indiscriminately can complicate forensic analysis.
At AGR Technology, we help businesses improve their incident readiness before an event occurs. That may include security monitoring guidance, response planning, infrastructure review, and practical containment procedures tailored to your environment. If your organisation needs a more structured ransomware response capability, we can help you build it.
Recovery Strategies That Reduce Operational And Financial Damage
Recovery is not just about getting systems running again. It is about restoring operations safely, validating data integrity, and reducing the chance of a repeat incident. A rushed recovery can reintroduce malware, preserve attacker access, or restore corrupted data into production.
A stronger recovery strategy balances urgency with control.
Restoring Systems Safely And Verifying Data Integrity
Before restoration starts, businesses need confidence that the root cause has been identified and containment is holding. Recovery should usually follow a prioritised sequence based on business-critical services.
That process may include:
- Rebuilding affected systems from clean, trusted sources
- Resetting passwords and reviewing privileged access paths
- Scanning restored systems for persistence mechanisms or hidden malware
- Verifying backup integrity before reintroducing data
- Testing critical applications and dependencies before full production rollout
- Confirming that monitoring and logging are active during recovery
Data integrity matters just as much as system availability. If financial records, customer information, operational data, or configuration files have been altered, the business impact can continue long after systems appear normal.
Improving The Business Continuity Plan After An Attack
A ransomware incident should lead to meaningful improvement, not just a return to business as usual. Post-incident review helps businesses strengthen both security and resilience.
Important recovery and continuity actions include:
- Documenting what happened, what was affected, and how the response performed
- Updating the incident response plan based on lessons learned
- Tightening technical controls around the original access path
- Reassessing recovery time objectives and backup frequency
- Reviewing supplier dependencies and communication workflows
- Running tabletop exercises to test decision-making under pressure
This is also the point where many businesses decide to modernise outdated infrastructure, improve segmentation, or strengthen cloud and endpoint management. In practice, the best recovery plans are tied closely to broader IT strategy.
AGR Technology supports businesses with practical technology planning, security-focused system improvements, and tailored digital solutions that help reduce operational risk. If you need help improving resilience after an incident or want to prepare before one happens, speak with our team.
Conclusion
Ransomware defence works best when prevention, detection, response, and recovery are treated as connected parts of the same strategy. Businesses that rely on scattered tools or outdated processes often discover the gaps only after an incident has already caused disruption.
A more practical approach is to reduce attack surfaces, strengthen access controls, monitor for early warning signs, and make sure backups and recovery plans are genuinely usable. That is how businesses improve resilience in the real world.
At AGR Technology, we work with organisations that want clear, actionable support across cyber security, infrastructure, software, and digital operations. If your business needs help assessing ransomware risk, improving protective controls, or planning a stronger recovery capability, contact AGR Technology to start the conversation.
Ransomware Defense: Frequently Asked Questions
What makes ransomware a critical threat to businesses today?
Ransomware threatens businesses by disrupting operations, stealing data, causing financial losses, and damaging reputation. It targets essential systems and data, impacting companies of all sizes due to weak passwords, unpatched software, or phishing attacks.
How can businesses prevent ransomware attacks effectively?
Effective prevention involves layered security: enforcing multi-factor authentication, applying least-privilege access, hardening endpoints, filtering phishing emails, timely patching, network segmentation, and maintaining secure, tested backups.
What are common early warning signs of a ransomware infection?
Early signs include unusual login activities, new unexpected admin accounts, disabled antivirus or backup services, spikes in file encryption-like activities, suspicious PowerShell or command-line use, and unexpected data transfers.
Why is early detection important in ransomware defense?
Early detection limits damage by enabling quick containment before attackers encrypt or steal data. It helps stop lateral movement, preserve backups, and reduce operational disruption and recovery costs.
What strategies improve recovery after a ransomware attack?
Recovery should prioritize safe system restoration from trusted sources, verifying data integrity, resetting privileges, scanning for persistent threats, testing critical applications, and updating incident response plans based on lessons learned.
Are small and mid-sized businesses at risk of ransomware attacks?
Yes, small and mid-sized businesses are often targeted due to fewer security resources, inconsistent patching, weaker access controls, and limited incident response planning, making effective ransomware defense critical regardless of business size.
More solutions & content:
Unified Cyber Threat Management Solutions
Expert Penetration Testing Services in Australia
Cyber Security Services For Small Businesses
Cyber Security Services For Franchises
Cyber Security Audits for Clinics
Cyber Security Services For Healthcare Companies
Cyber Security Incident Response And Simulated Phishing Attacks
Essential Eight Compliance Services
Cyber Security Review (CSR) Services
Cloud Application Security Services

Alessio Rigoli is the founder of AGR Technology and got his start working in the IT space originally in Education and then in the private sector helping businesses in various industries. Alessio maintains the blog and is interested in a number of different topics emerging and current such as Digital marketing, Software development, Cryptocurrency/Blockchain, Cyber security, Linux and more.
Alessio Rigoli, AGR Technology
![logo-new-23[1] logo-new-23[1]](https://cdn-ihdfn.nitrocdn.com/eZVJvoSTyVixkEUySRKiaseNtUlmgCyu/assets/images/optimized/rev-b7ced37/agrtech.com.au/wp-content/uploads/elementor/thumbs/logo-new-231-qad2sqbr9f0wlvza81xod18hkirbk9apc0elfhpco4.png)






